Problem
Small organizations in Malawi run networks with no security posture visibility. They can't afford enterprise security tools, and free CLI tools produce raw output that non-technical stakeholders can't act on.
Solution
VulnMapper wraps Nmap for port/service discovery and integrates with the NIST NVD CVE database API to map discovered services to known vulnerabilities. Results are stored in SQLite and surfaced through a Flask web UI with exportable HTML/PDF reports with risk severity ratings.
Real-World Impact
Used in a mock security audit for a Mzuzu University lab network. Identified 3 critical misconfigurations including an exposed admin panel and outdated SSH daemon.
Challenges Faced
Rate limiting on NIST NVD API required implementing a local CVE cache with TTL. Parsing Nmap XML output reliably across different OS/network environments was more complex than expected.
Key Learnings
Security tools need to communicate risk clearly — not just find it. A scanner that produces a 500-line raw dump that no one reads is useless. The report design was as important as the scan logic.
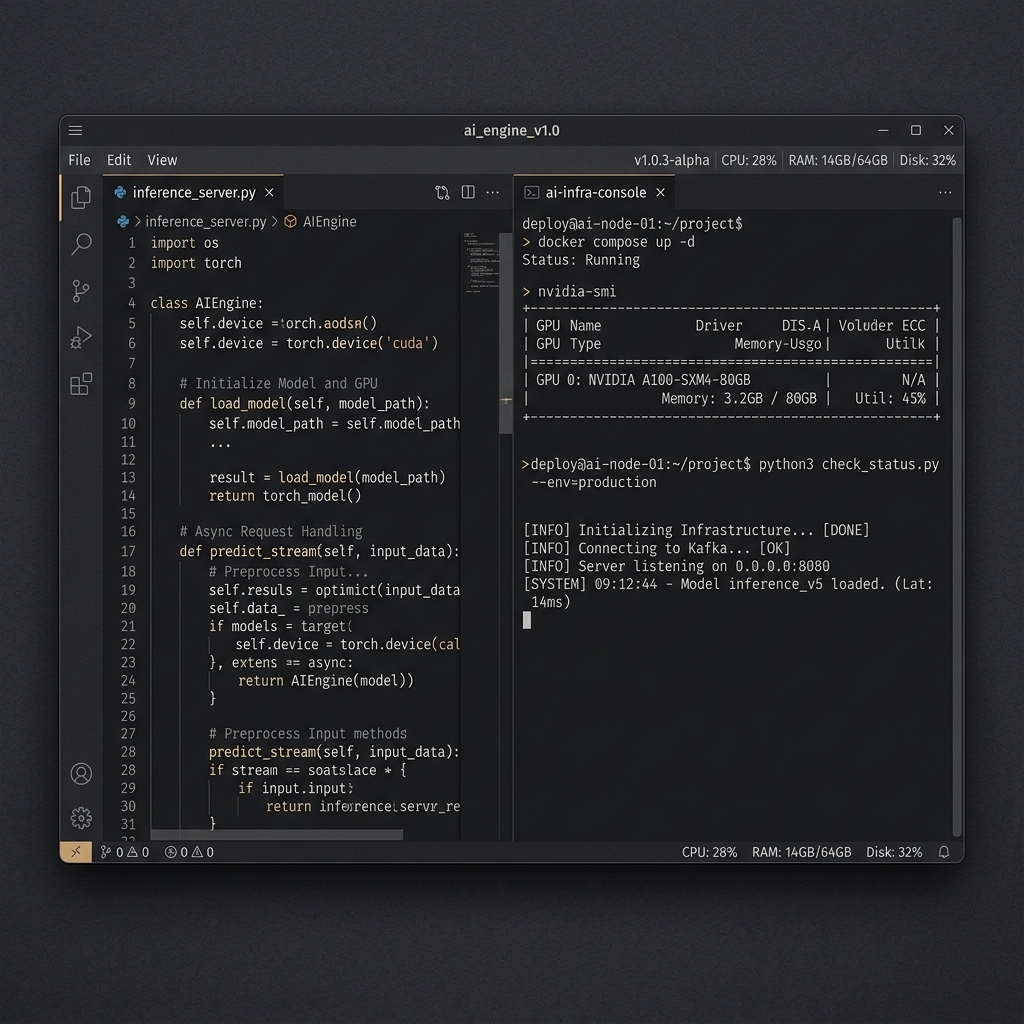
Demo & Execution Screenshots